Search for "henk" returned 172 results

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
55 min
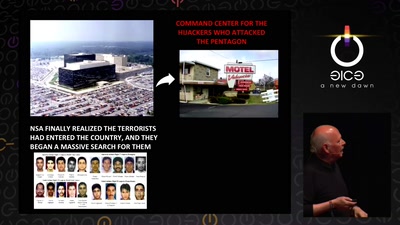
Attribution revolution
Turning copyright upside-down with metadata
61 min
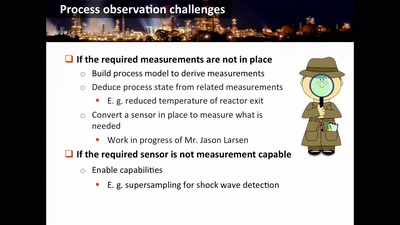
Damn Vulnerable Chemical Process
Exploitation in a new media

62 min
HUMUS sapiens
Open Soil Research
50 min
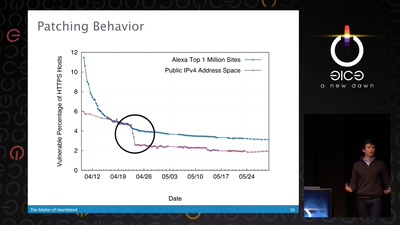
The Matter of Heartbleed
What went wrong, how the Internet reacted, what we can…
57 min
"Fluxus cannot save the world."
What hacking has to do with avantgarde art of the 1960ies…
44 min
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
60 min
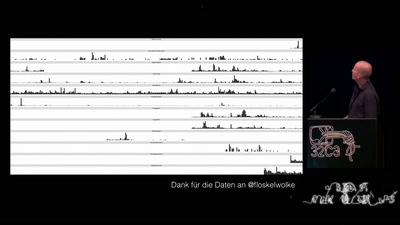
„Nach bestem Wissen und Gewissen“ – Floskeln in der Politik
Politische Phrasologie – warum man aus dem ganzen Zeug, das…
95 min
Platform System Interface
Design und Evaluation holistischer Computerarchitektur
61 min
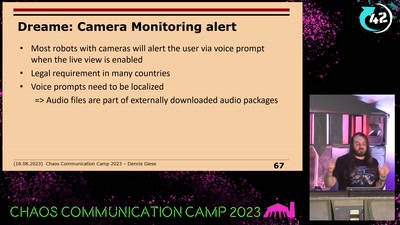
Vacuum robot security and privacy
prevent your robot from sucking your data
56 min
Making Technology Inclusive Through Papercraft and Sound
Introducing the Love to Code Platform

53 min
Hacken Dicht
Die Aftershow-Party
62 min
Tell no-one
A century of secret deals between the NSA and the telecom…

57 min
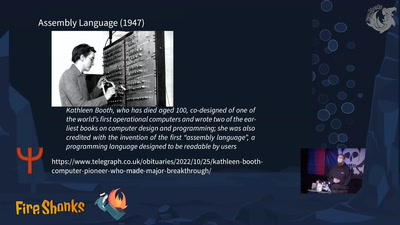
Everything you want to know about x86 microcode, but might have been afraid to ask
An introduction into reverse-engineering x86 microcode and…
51 min