Search for "olf" returned 7522 results
45 min
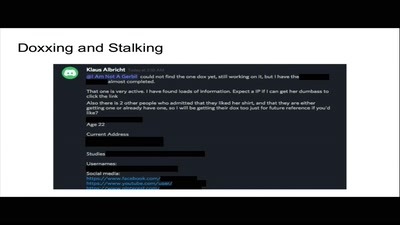
Privacy: An Unequally Distributed Resource
A Study of Privacy as Privilege in Our World
32 min
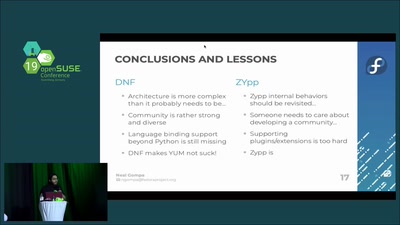
DNF vs ZYpp: Fight!
A comparison of the two major RPM package managers
57 min
Cryptowars 2.0: Lessons from the past, for the present
It's not only Hollywood who is out of ideas
28 min
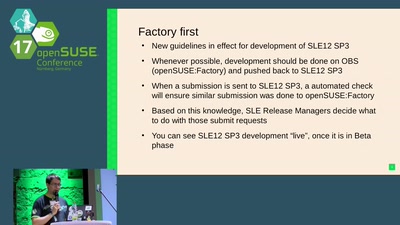
Bridging openSUSE and SLE gap, part deux
Return of the GNOME, part deux aka the revenge

66 min
Podjournalism
The Role of Podcasting in Critical and Investigative…
38 min
Squeezing Attack Traces
How to get useable information out of your honeypot
52 min
The Youth Hostel
An odyssey in the margins of software and paper

34 min
Digital Musical Instruments
Evolution and design of new interfaces for musical…
56 min
Hacking ideologies, part 2: Open Source, a capitalist movement
Free Software, Free Drugs and an ethics of death
82 min
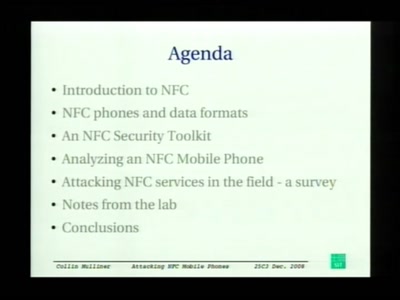
Attacking NFC mobile phones
First look at the security of NFC mobile phones
30 min
NexMon - Make Wi-Fi hacking on smartphones great again!
Reverse engineering of the Nexus 5 Wi-Fi chip
58 min
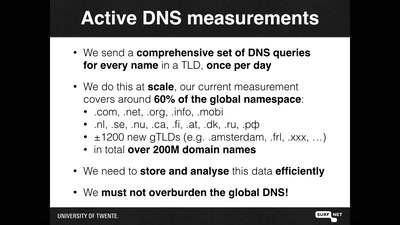
OpenINTEL: digging in the DNS with an industrial size digger
I measured 60% of the DNS, and I found this
32 min
Is this the Mobile Gadget World We Created?
The story of the world's first socially responsible mobile…
52 min
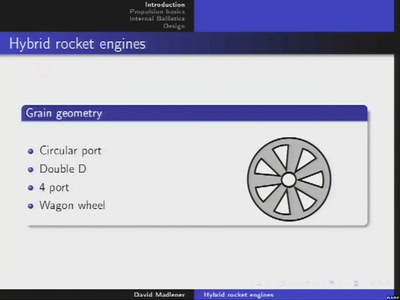
Hybrid rocket engines
Design and implementation of rocket engines with two-phase…
62 min
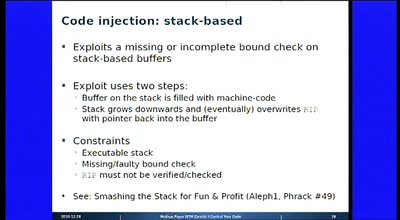
I Control Your Code
Attack Vectors Through the Eyes of Software-based Fault…
26 min
ChokePointProject - Quis custodiet ipsos custodes?
Aggregating and Visualizing (lack of) Transparancy Data in…
47 min
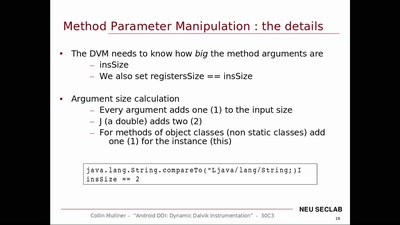
Android DDI
Dynamic Dalvik Instrumentation of Android Applications and…
51 min
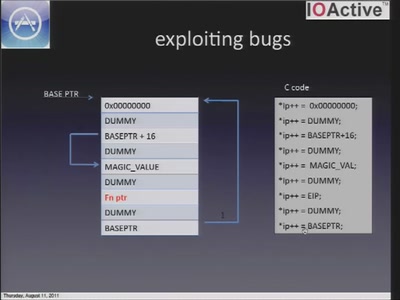
iOS application security
A look at the security of 3rd party iOS applications
35 min
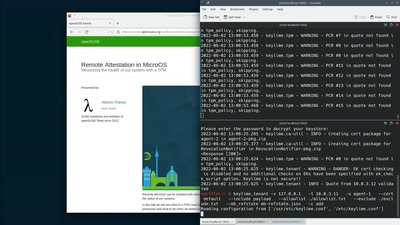
Remote Attestation in MicroOS
Measuring the health of our system with a TPM
41 min
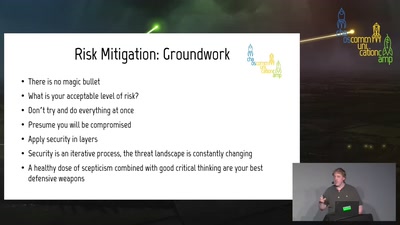
Introduction to (home) network security.
A beginner-friendly guide to network segmentation for…
30 min
Love, CyBorgs, Art and Open Source – an artistic approach on how to stay golden
How to educate society through the language of art
45 min
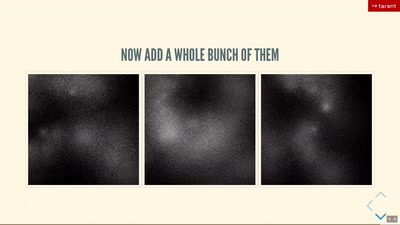
Generating uniqueness
How generative art pushes the boundaries of intellectual…
58 min
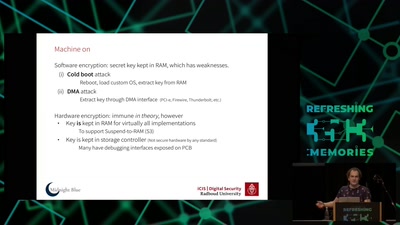
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)

60 min
Fictional panel discussion: Let Nature Rule
Exploring solutions and impacts of automated environmental…
31 min