Search for "mh" returned 3038 results
60 min
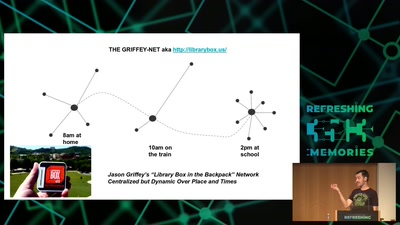
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…

39 min
The Eye on the Nile
Egypt's Civil Society Under Attack
40 min
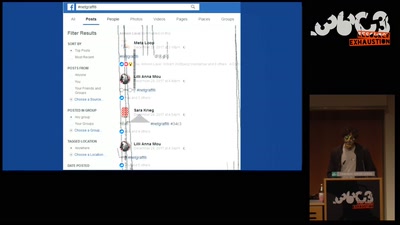
Art against Facebook
Graffiti in the ruins of the feed and the…
26 min
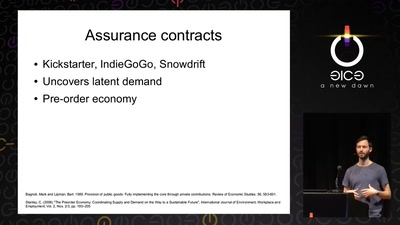
Technomonopolies
How technology is used to subvert and circumvent…
53 min
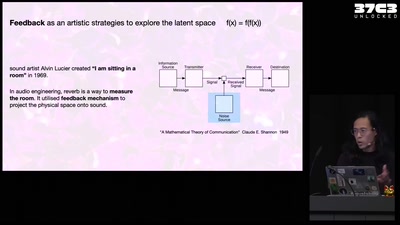
Self-cannibalizing AI
Artistic Strategies to expose generative text-to-image…
60 min
Lifting the Fog on Red Star OS
A deep dive into the surveillance features of North Korea's…
47 min
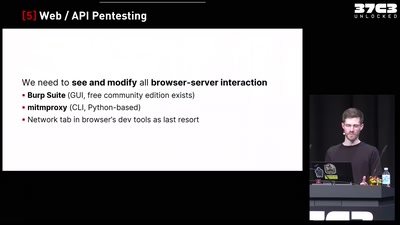
Finding Vulnerabilities in Internet-Connected Devices
A Beginner’s Guide
31 min
BGP and the Rule of Custom
How the internet self-governs without international law
54 min
How hackers grind an MMORPG: by taking it apart!
An introduction to reverse engineering network protocols
55 min
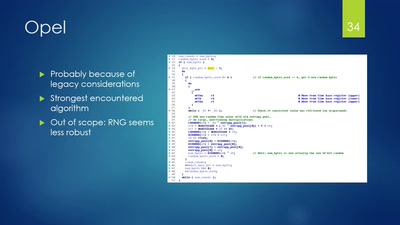
Vehicle immobilization revisited
Uncovering and assessing a second authentication mechanism…
43 min
Seeds of Change
Unlearning & Radical Collective Change in Online Communities

60 min
Attacking end-to-end email encryption
Efail, other attacks and lessons learned.
63 min
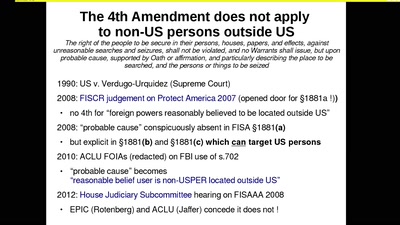
The Cloud Conspiracy 2008-2014
how the EU was hypnotised that the NSA did not exist
30 min
Privacy and Consumer Markets
Reversing the Surveillance Business Model
39 min