Search for "Mo" returned 10406 results

62 min
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…

63 min
The Global Assassination Grid
The Infrastructure and People behind Drone Killings
44 min
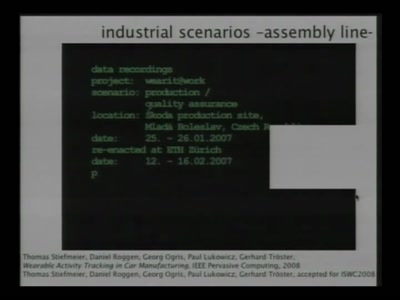
About Cyborgs and Gargoyles
State of the Art in Wearable Computing

44 min
Just Estonia and Georgia?
Global-scale Incident Response and Responders
49 min
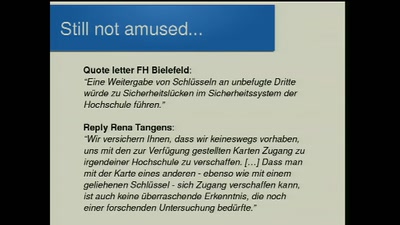
Men who stare at bits
RFID-Studierendenkarten mit Fehlern

60 min
The Grand EU Data Protection Reform
A latest battle report by some key actors from Brussels
56 min
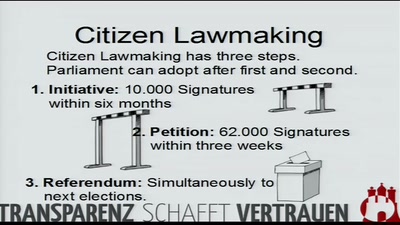
We are all lawmakers!
How to further transparency by law – the Hamburg example…
45 min
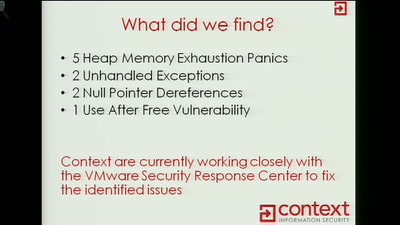
ESXi Beast
Exploiting VMWARE ESXi Binary Protocols Using CANAPE
23 min
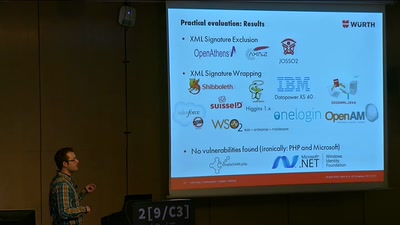
On Breaking SAML
Be Whoever You Want to Be
59 min
Lightning Talks Day3 - Morning
4 minutes of fame

63 min
Writing a Thumbdrive from Scratch
Prototyping Active Disk Antiforensics
28 min
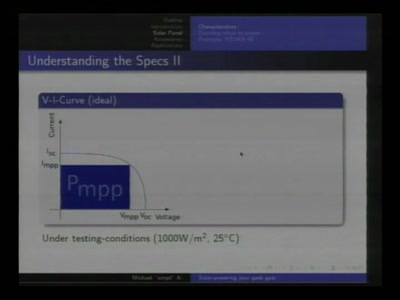
Solar-powering your Geek Gear
Alternative and mobile power for all your little toys

50 min
Fnord News Show (English interpretation)
We help in seeing teh Fnords
52 min
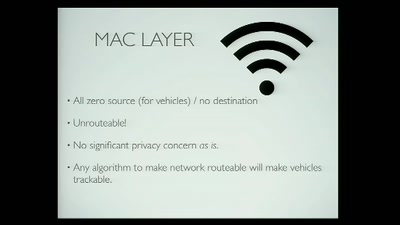
Privacy and the Car of the Future
Considerations for the Connected Vehicle
59 min
Meldegesetz
Was aus dem 57-Sekunden-Gesetz wurde
54 min
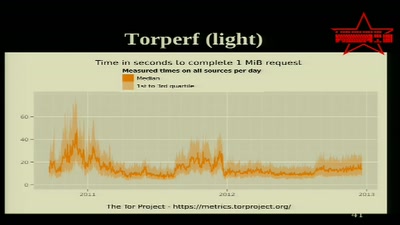
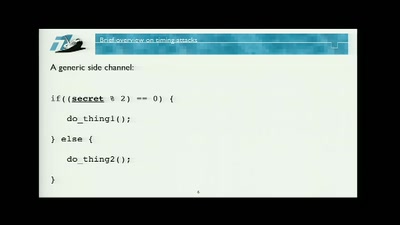
Time is NOT on your Side
Mitigating Timing Side Channels on the Web
57 min
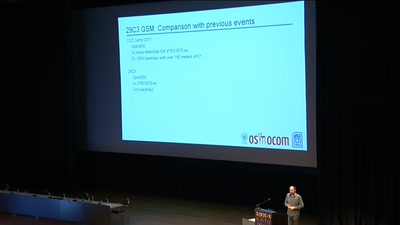
29C3 GSM: Cell phone network review
262 42 - The full spectrum
68 min
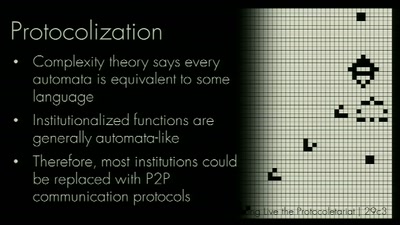
The future of protocol reversing and simulation applied on ZeroAccess botnet
Mapping your enemy Botnet with Netzob
53 min
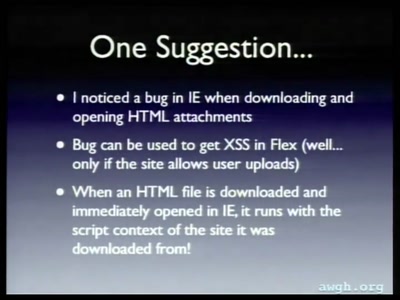
Short Attention Span Security
A little of everything
45 min