Search for "olf" returned 7527 results

64 min
Are Whistleblowers safer today than they were at OHM2013?
Current case studies of whistleblowing in Europe, and how…
115 min
Passive covert channels in the Linux kernel
Implementation and detection of kernel based backdoors and…

30 min
The Magical Secrecy Tour
A Bus Trip into the Surveillance Culture of Berlin One Year…
63 min
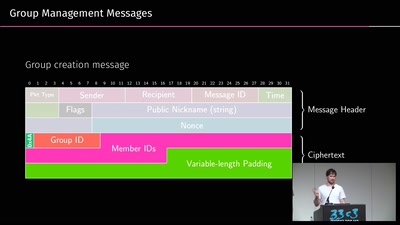
A look into the Mobile Messaging Black Box
A gentle introduction to mobile messaging and subsequent…
30 min
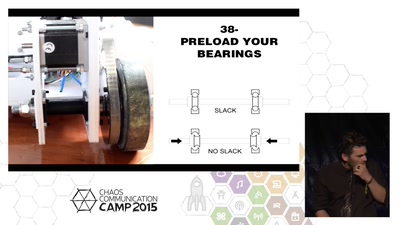
A practical prototyping primer
A rather unstructured selection of things I wished I knew…

65 min
Terrorist All-Stars
Some cases of terrorism around the world that are not…
59 min
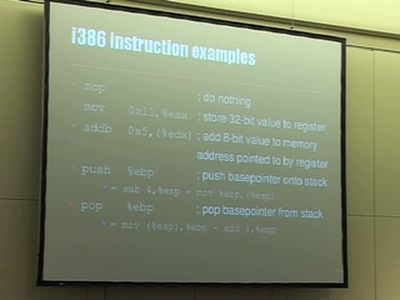
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…
34 min
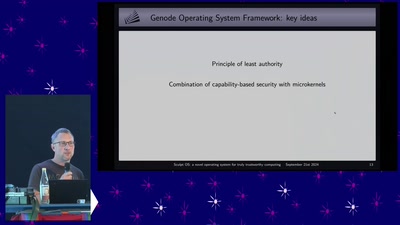
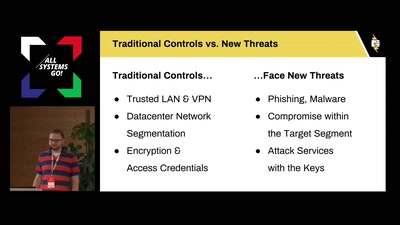
Little Services, Big Risks
Extending capability-based security models to achieve…
31 min
Law Enforcement Are Hacking the Planet
How the FBI and local cops are hacking computers outside of…
30 min
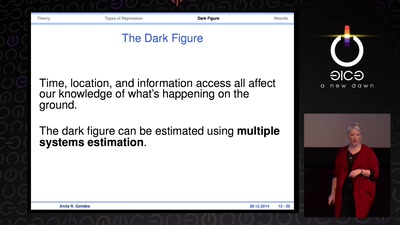
Information Control and Strategic Violence
How governments use censorship and surveillance as part of…
71 min
Introduction to Satellite Communications
the joy and challange of operating satellite communication…
59 min
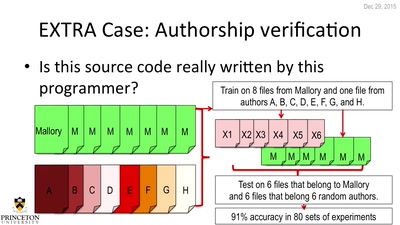
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
41 min
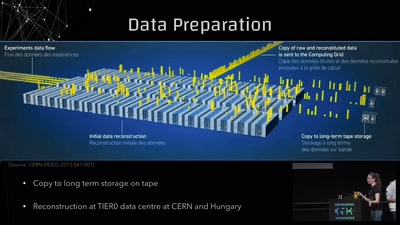
Conquering Large Numbers at the LHC
From 1 000 000 000 000 000 to 10: Breaking down 14 Orders…

36 min
Parkour communications
How you can communicate, free running style, using nothing…
security in 2006: having phun with it.jpg)
111 min
X.25 (in)security in 2006: having phun with it
Actual present, next future & field experiences analysis of…
57 min
"Fluxus cannot save the world."
What hacking has to do with avantgarde art of the 1960ies…
47 min
Hardening hardware and choosing a #goodBIOS
Clean boot every boot - rejecting persistence of malicious…
40 min
Art against Facebook
Graffiti in the ruins of the feed and the…

68 min
Weaponizing Cultural Viruses
A Manual For Engaged Memetic Resistance on The Front Lines…

31 min