Search for "Ana" returned 10009 results
57 min
Why Net Neutrality Matters?
Status update on current legislation, campaigns and actions
30 min
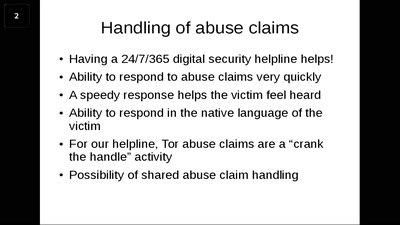
A Torifying Tale
Our experiences of building and running Tor servers

51 min
How to contribute to make open hardware happen
Mooltipass, Openpandora/Pyra and Novena/Senoko: how I…

14 min
Why openSUSE is the perfect OS for handhelds
And how to bring openSUSE to your device as well!
62 min
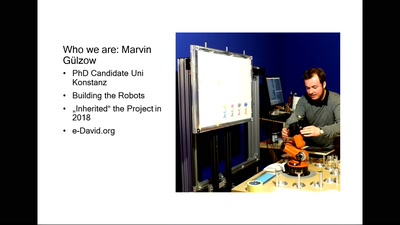
Transhuman Expression
Interdisciplinary research in Painting and Robotics. with…
32 min
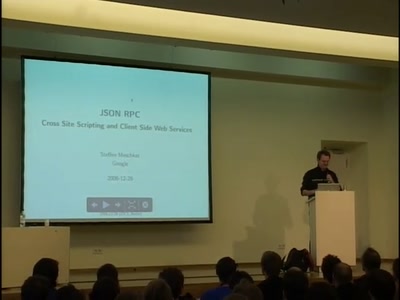
spispy: SPI flash device emulation
Open source tools for flash emulation and research
60 min
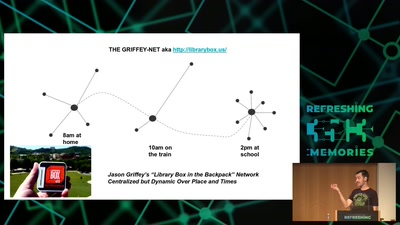
Wind: Off-Grid Services for Everyday People
Integrating nearby and offline connectivity with the…

46 min
Digital Airwaves
Software Defined Radio Basics and some Modulation Theory
47 min
The Realm of Too Many Options
Write, record, mix and actually finish your music
24 min
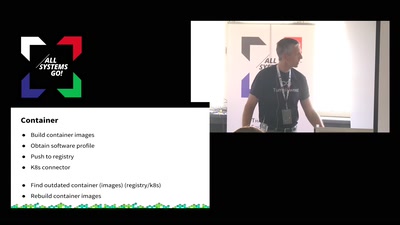
From Physical to Cloud to Container
One system to deploy and manage them all
20 min
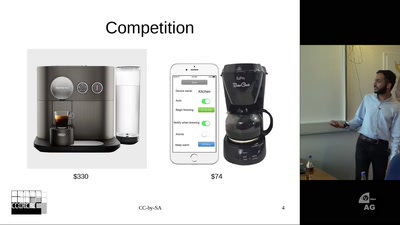
HTCPCP - Networking your Coffeepot
IoT done right for fun and no profit
35 min
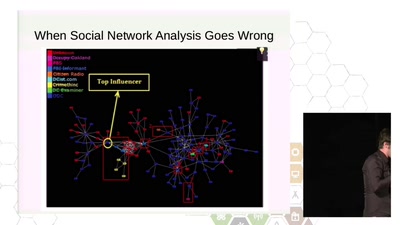
Weaponized Social
Understanding and tools to mitigate network-scale violences

59 min
8 Years of Config Management
a journey through one company's challenges and learnings
98 min
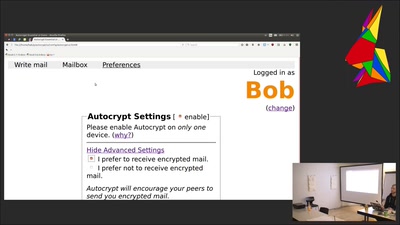
Towards automatic end to end mail encryption
mail encryption overview and hands-on Autocrypt sessions

43 min
Pirate Radio
Running a Station and Staying on the Air

30 min
Closing Event
So long and thanks for all the fish

48 min
All Tomorrow's Condensation
A steampunk puppet extravaganza by monochrom and friends
55 min
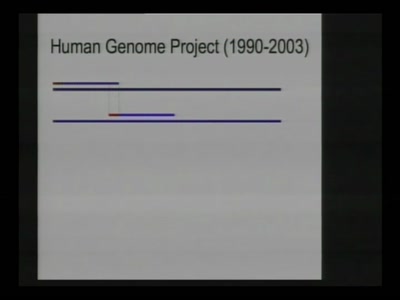
All your base(s) are belong to us
Dawn of the high-throughput DNA sequencing era

21 min
Closing Event
Good Bye and have a safe trip home!

61 min
Trustworthy secure modular operating system engineering
fun(ctional) operating system and security protocol…
![for women in "${tech[@]}"; do](https://static.media.ccc.de/media/conferences/camp2015/6774-hd.jpg)
26 min
for women in "${tech[@]}"; do
Let's talk, share and learn from each other.
60 min
Resisting Surveillance: it's is not just about the metadata
The infiltration and physical surveillance of social…
58 min
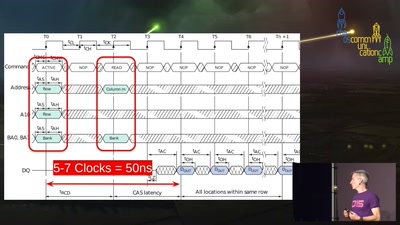
Advanced memory forensics: The Cold Boot Attacks
Recovering keys and other secrets after power off

47 min