Search for "Mo" returned 10605 results
59 min
Millions of Lessons Learned on Electronic Napkins
On the way to free(ing) education
42 min
IFG: Chance oder Bürgerbluff?
Informationsfreiheit in Deutschland. Ein Sachstand.
58 min
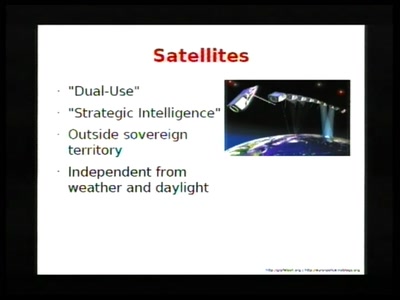
Collapsing the European security architecture
More security-critical behaviour in Europe!
63 min
Exploiting Symbian
Symbian Exploit and Shellcode Development
35 min
Ethics in the data society
Power and politics in the development of the driverless car
47 min
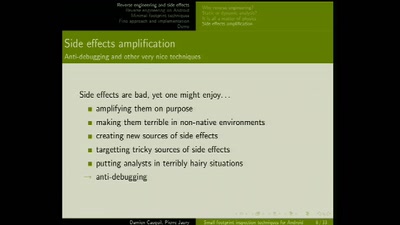
Small footprint inspection techniques for Android
Reverse engineering on Android platforms
61 min
Defend your Freedoms Online: It's Political, Stupid!
A Positive agenda against the next ACTA, SOPA, and such

48 min
SWF and the Malware Tragedy
Hide and Seek in A. Flash
45 min
Privacy in the social semantic web
Social networks based on XMPP
51 min
Algorithmic Music in a Box
Doing music with microcontrollers

126 min
Lightning Talks 1
5 Minutes of Fame
55 min
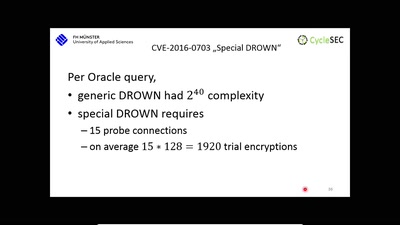
The DROWN Attack
Breaking TLS using SSLv2
55 min
Das Grundrecht auf digitale Intimsphäre
Festplattenbeschlagnahme in neuem Licht
54 min
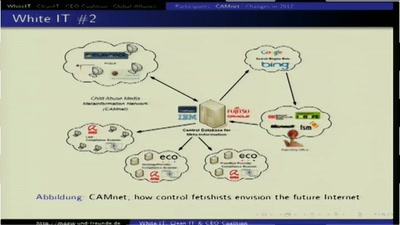
White IT, Clean IT & CEO Coalition
Wie die Exekutive versucht Provider zur Inhaltekontrolle im…
60 min
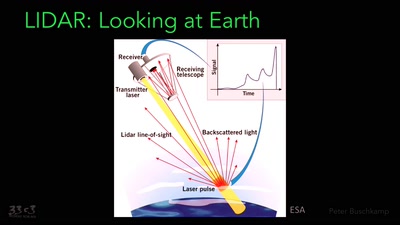
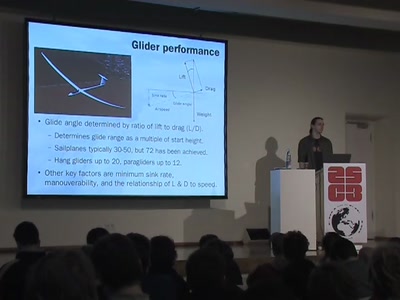
Flying for free
Exploiting the weather with unpowered aircraft
60 min
Der elektronische Personalausweis
Endlich wird jeder zum "Trusted Citizen"
51 min
Lightning Talks Day2
4 minutes of fame
94 min
Security Nightmares 2009
Oder: worüber wir nächstes Jahr lachen werden
52 min
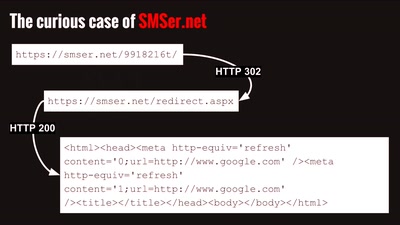
Securing the Campaign
Security and the 2012 US Presidential Election
53 min