Search for "Mo" returned 10528 results
53 min
Million Dollar Dissidents and the Rest of Us
Uncovering Nation-State Mobile Espionage in the Wild
65 min
eVoting after Nedap and Digital Pen
Why cryptography might not fix the issue of transparent…
82 min
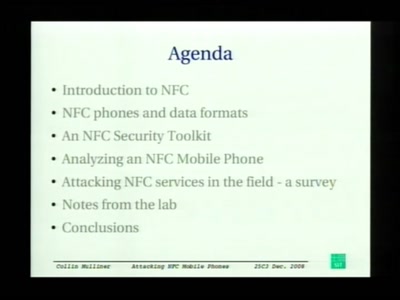
Attacking NFC mobile phones
First look at the security of NFC mobile phones
60 min
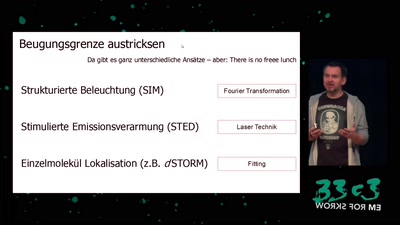
Es sind die kleinen Dinge im Leben
von Mikroskopen, Wahrnehmung und warum das kaum jemanden…

26 min
Hacking the World
The struggle for security for all.
67 min
Life is a Holodeck!
An overview of holographic techniques

70 min
Neusprech im Überwachungsstaat
Politikersprache zwischen Orwell und Online

52 min
Datenpannen
Forderungen nach dem Jahr der Datenverbrechen

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
38 min
Squeezing Attack Traces
How to get useable information out of your honeypot
61 min
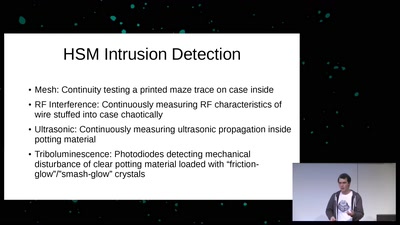
Untrusting the CPU
A proposal for secure computing in an age where we cannot…

56 min
Console Hacking 2008: Wii Fail
Is implementation the enemy of design?
99 min
Fnord-Jahresrückblick
Wir helfen euch, die Fnords zu sehen!
64 min
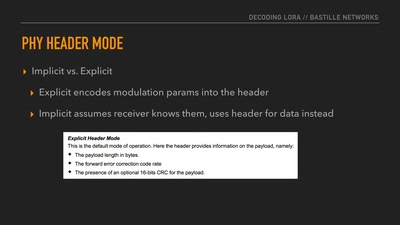
Decoding the LoRa PHY
Dissecting a Modern Wireless Network for the Internet of…
53 min
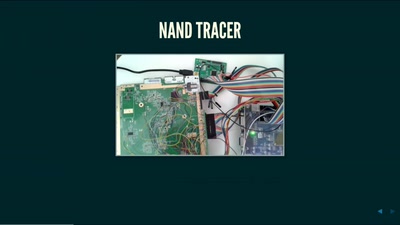
Console Hacking 2016
PS4: PC Master Race
61 min
Nintendo Hacking 2016
Game Over
60 min
Check Your Police Record!
Polizeiliche Datenbanken und was man über seinen Auskunfts-…
24 min