Search for "David" returned 316 results

59 min
Security of the IC Backside
The future of IC analysis

63 min
Das Assange-Auslieferungsverfahren
Als Prozessbeobachter in London

31 min
A Tale of Two Leaks:
How Hackers Breached the Great Firewall of China
60 min
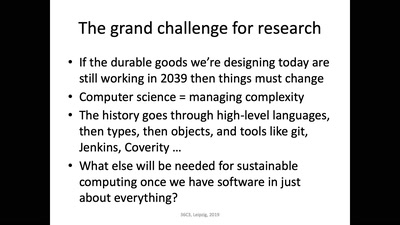
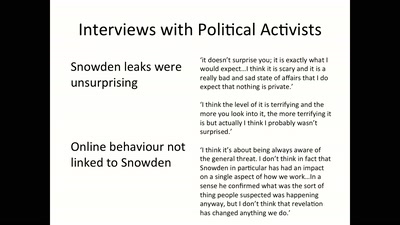
Media Coverage and the Public in the Surveillance Society
Findings from a Research Project on Digital Surveillance…

41 min
Chaos Communication Chemistry
DNA security systems based on molecular randomness

61 min
AlphaFold – how machine learning changed structural biology forever (or not?)
Getting first-hand insights into the impact of machine…
63 min
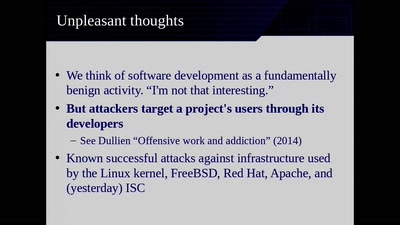
Reproducible Builds
Moving Beyond Single Points of Failure for Software…
54 min
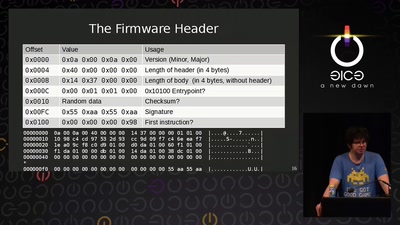
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?
57 min
Hello World!
How to make art after Snowden?

60 min
Routerzwang und Funkabschottung
Was Aktivisten davon lernen können
47 min
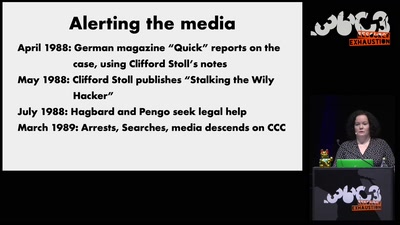
The KGB Hack: 30 Years Later
Looking back at the perhaps most dramatic instance of…

59 min
Hacking EU funding for a decentralizing FOSS project
Understanding and adapting EU legal guidelines from a FOSS…

61 min