Search for "Wetter" returned 2428 results
43 min
No PoC? No Fix! - A sad Story about Bluetooth Security
It is just a broken memcpy in the Bluetooth stack. Do we…
44 min
ASLR on the line
Practical cache attacks on the MMU
44 min
Exploiting PHP7 unserialize
teaching a new dog old tricks
36 min
Understanding the Snooper’s Charter
Theresa May’s effort to abolish privacy
58 min
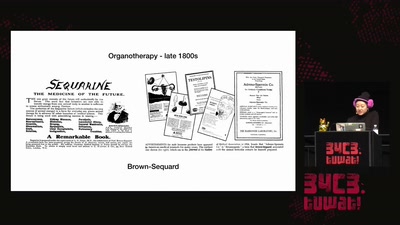
Open Source Estrogen
From molecular colonization to molecular collaboration

51 min
Funky File Formats
Advanced binary tricks
43 min
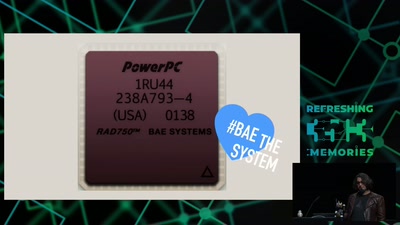
The Mars Rover On-board Computer
How Curiosity's Onboard Computer works, and what you can…
31 min
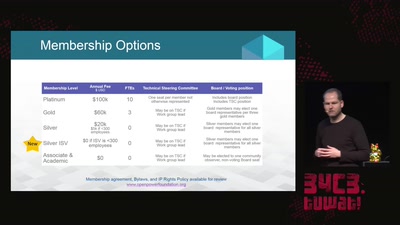
openPower - the current state of commercial openness in CPU development
is there no such thing as open hardware?
29 min
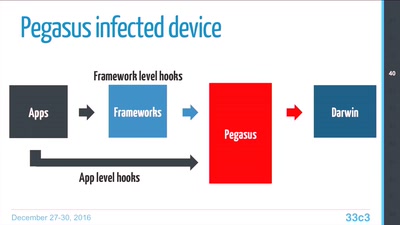
Pegasus internals
Technical Teardown of the Pegasus malware and Trident…
33 min
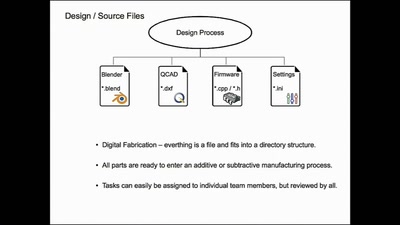
Structuring open hardware projects
experiences from the “i3 Berlin” 3D printer project with…
39 min
Web-based Cryptojacking in the Wild
When your browser is mining coins for other people
58 min
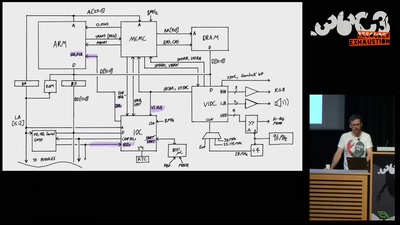
The Ultimate Acorn Archimedes talk
Everything about the Archimedes computer (with zero…

45 min
HbbTV Security
OMG - my Smart TV got pr0wn3d
56 min
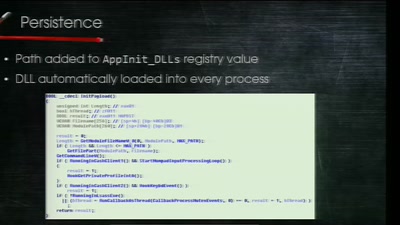
Electronic Bank Robberies
Stealing Money from ATMs with Malware
46 min
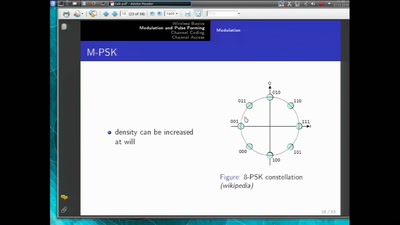
Basics of Digital Wireless Communication
introduction to software radio principles

60 min
Are machines feminine?
exploring the relations between design and perception of…

57 min
Everything you want to know about x86 microcode, but might have been afraid to ask
An introduction into reverse-engineering x86 microcode and…
63 min