Search for person "Paul Wouters" returned 87 results
41 min
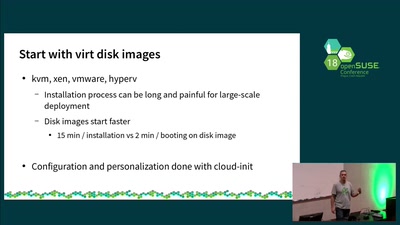
Your first steps with openSUSE Kubic
Practical information on how to get started with openSUSE…
27 min
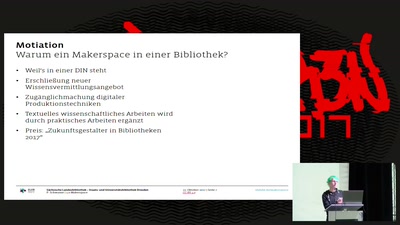
SLUB Makerspace
Wissen kommt von machen

31 min
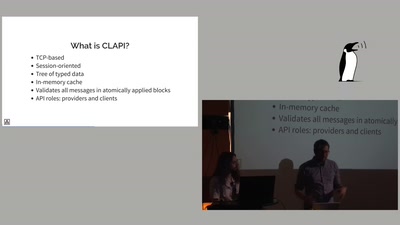
Demystifying Network Cards
Things you always wanted to know about NIC drivers

55 min
Netzphilosophische Matinée
Ein Hirnlüfter der Dresdner Technikphilosophie.…
61 min
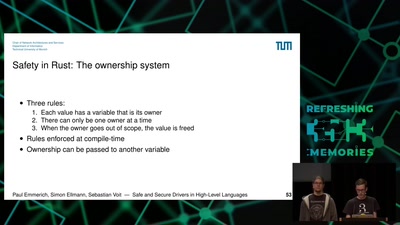
Safe and Secure Drivers in High-Level Languages
How to write PCIe drivers in Rust, go, C#, Swift, Haskell,…

10 min
Elevator_Madness
Jugend hackt Ulm 2017
41 min
Rise of the Machines: Sie beginnen zu lernen.
Woher Amazon weiß, für was du dich als nächstes…
30 min
All Our Shared Spectrum Are Belong to Us
Visualizing WLAN Channel Usage on OpenWRT
61 min