Search for "mel" returned 2579 results
60 min
Lets break modern binary code obfuscation
A semantics based approach
47 min
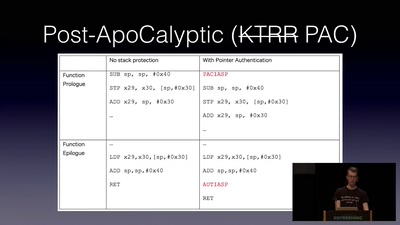
Jailbreaking iOS
From past to present
60 min
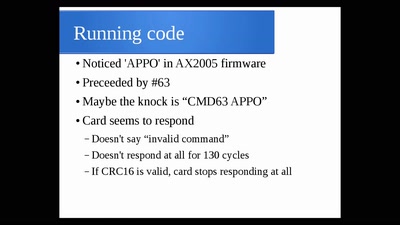
The Exploration and Exploitation of an SD Memory Card
by xobs & bunnie
25 min
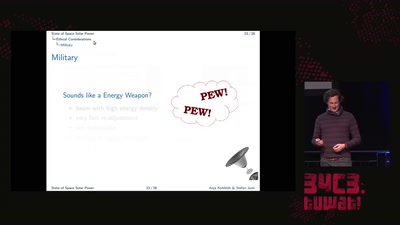
Saving the World with Space Solar Power
or is it just PEWPEW?!
31 min
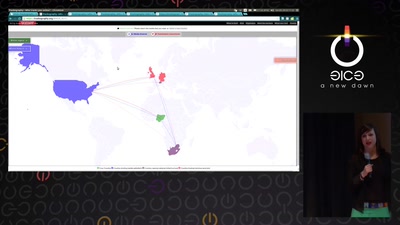
Trackography
You never read alone

37 min
The foodsaving grassroots movement
How cooperative online structures can facilitate…
63 min
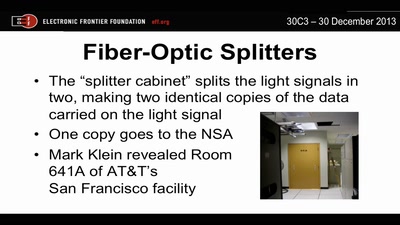
Through a PRISM, Darkly
Everything we know about NSA spying

33 min
Global Civil Society Under Attack
Reports from the Frontlines
49 min
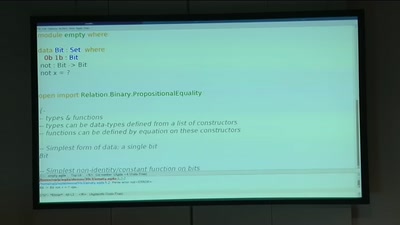
BREACH in Agda
Security notions, proofs and attacks using dependently…
64 min
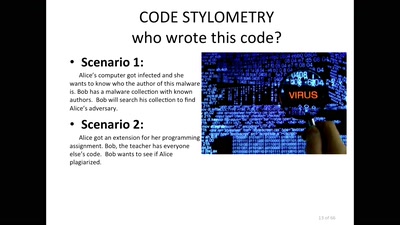
Source Code and Cross-Domain Authorship Attribution
The Role of Stylometry in Privacy
55 min
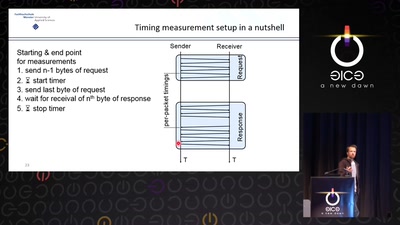
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
61 min
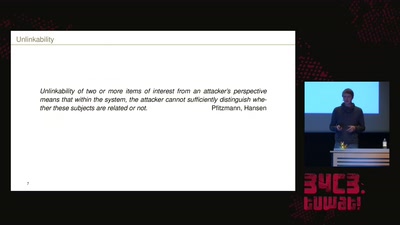
How Alice and Bob meet if they don't like onions
Survey of Network Anonymisation Techniques
58 min
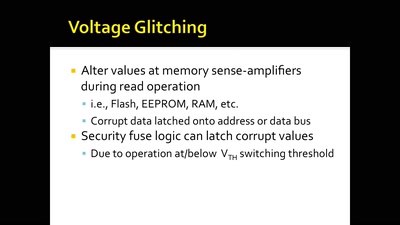
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets
44 min
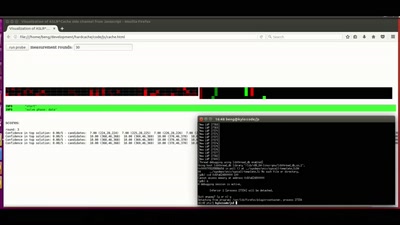
ASLR on the line
Practical cache attacks on the MMU
47 min
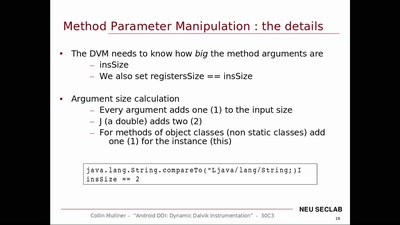
Android DDI
Dynamic Dalvik Instrumentation of Android Applications and…

72 min