Search for "ths" returned 9152 results

46 min
Automated Exploit Detection in Binaries
Finding exploitable vulnerabilities in binaries
49 min
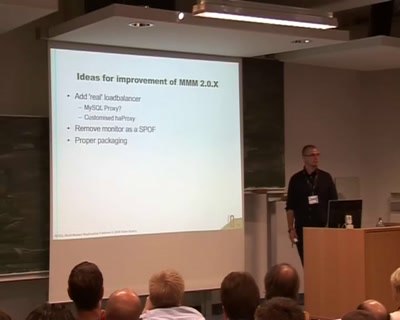
MySQL Multi-Master Replication Failover - A step-by-step explanation
How to setup a MySQL cluster with Automatic failover for HA

49 min
Hacking Data Retention
How bureaucrats fail to fight terror
38 min
GIS features in MariaDB and MySQL
What has happened in recent years ...

53 min
Automated Botnet Detection and Mitigation
How to find, invade and kill botnets automated and…
34 min
Ling - High level system programming
modular and precise resource management
57 min
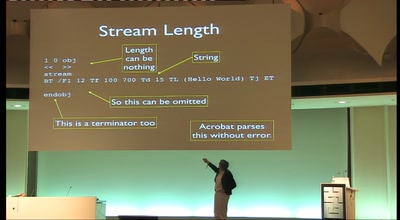
OMG WTF PDF
What you didn't know about Acrobat
59 min
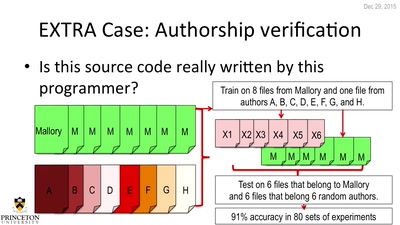
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…

61 min
Net Neutrality in Europe
alea iacta est
35 min
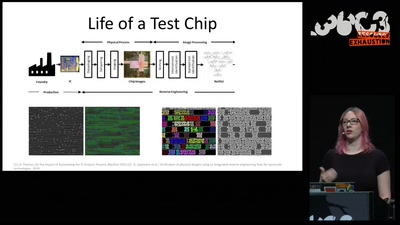
Understanding millions of gates
Introduction to IC reverse engineering for…
50 min