Search for "Jim" returned 5093 results

37 min
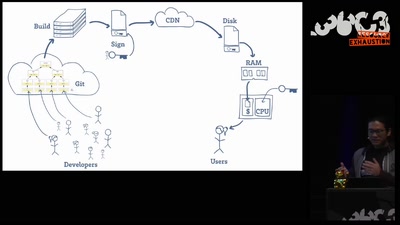
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
60 min
Open Source is Insufficient to Solve Trust Problems in Hardware
How Betrusted Aims to Close the Hardware TOCTOU Gap
61 min
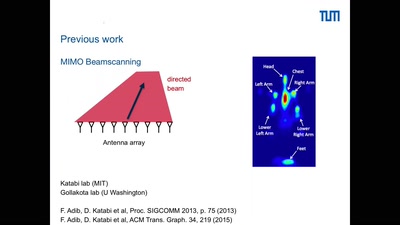
Holography of Wi-Fi radiation
Can we see the stray radiation of wireless devices? And…
55 min
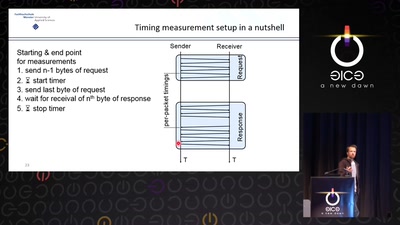
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks
61 min
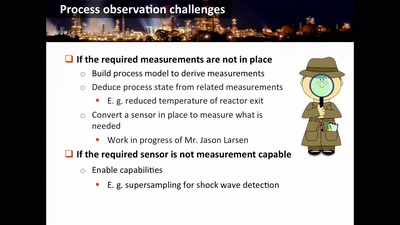
Damn Vulnerable Chemical Process
Exploitation in a new media
46 min
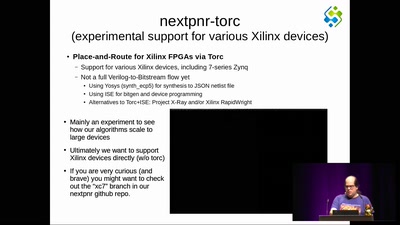
The nextpnr FOSS FPGA place-and-route tool
the next step forward in open source FPGA tools

61 min
"The" Social Credit System
Why It's Both Better and Worse Than We can Imagine
56 min
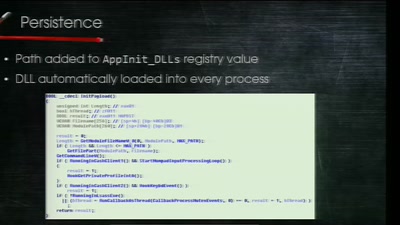
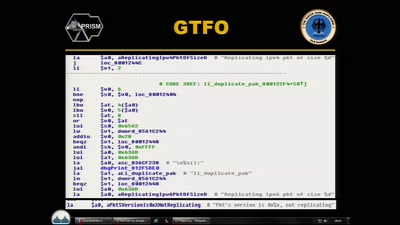
Electronic Bank Robberies
Stealing Money from ATMs with Malware
43 min
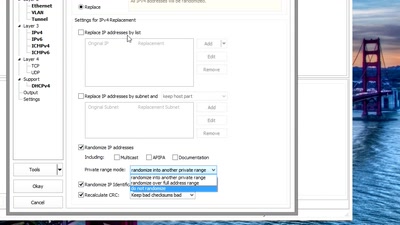
Sanitizing PCAPs
Fun and games until someone uses IPv6 or TCP
45 min
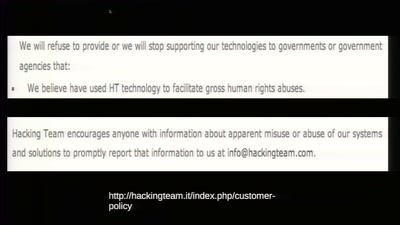
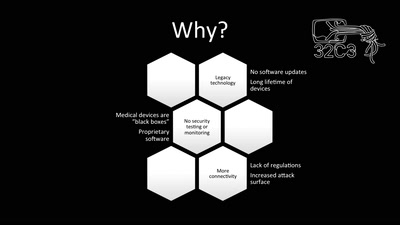
To Protect And Infect
The militarization of the Internet
55 min
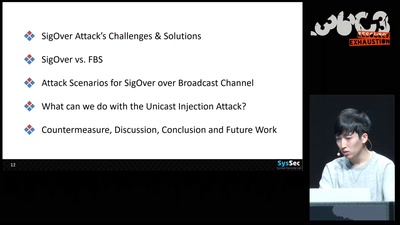
SigOver + alpha
Signal overshadowing attack on LTE and its applications
46 min
CounterStrike
Lawful Interception
54 min
How medicine discovered sex
Introduction to sex- and gender-sensitive medicine
40 min
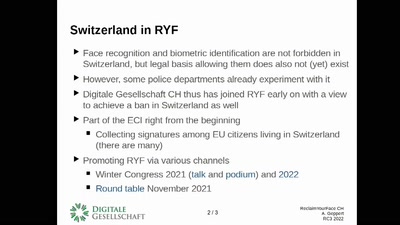
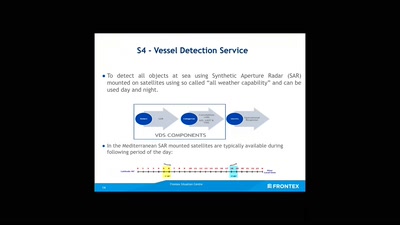
No roborders, no nation, or: smile for a European surveillance propagation
How an agency implements Fortress Europe by degrading…

56 min
Household, Totalitarianism and Cyberspace
Philosophical Perspectives on Privacy Drawing on the…
60 min