Search for "Seth Hardy" returned 901 results
32 min
History and implications of DRM
From tractors to Web standards

46 min
Remo2hbo -Robustes und reparierbares Vitalparametermonitoring
Medizingeräte für Alle
61 min
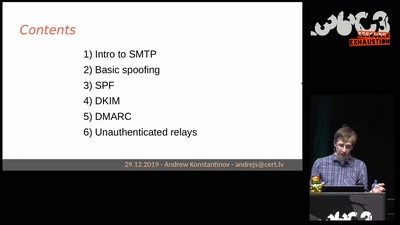
Email authentication for penetration testers
When SPF is not enough

30 min
The Magical Secrecy Tour
A Bus Trip into the Surveillance Culture of Berlin One Year…
54 min
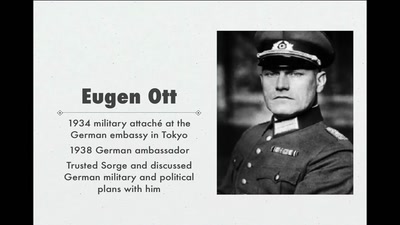
World War II Hackers
Stalin's best men, armed with paper and pen
56 min
Planes and Ships and Saving Lives
How soft and hardware can play a key role in saving lives…
60 min
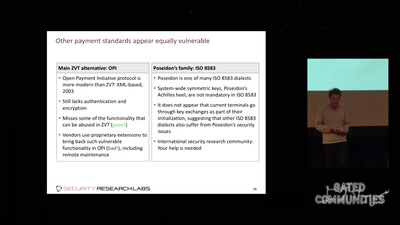
Shopshifting
The potential for payment system abuse
59 min
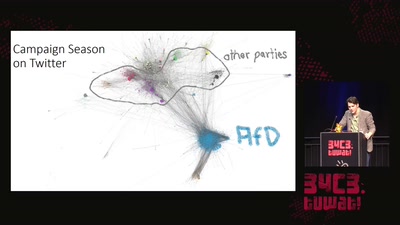
Pointing Fingers at 'The Media'
The Bundestagswahl 2017 and Rise of the AfD
62 min
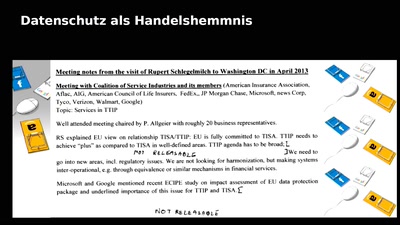
Deine Rechte sind in diesen Freihandelsabkommen nicht verfügbar
Der Protest gegen TTIP und CETA

39 min
The Eye on the Nile
Egypt's Civil Society Under Attack
58 min
Hack_Curio
Decoding The Cultures of Hacking One Video at a Time
58 min
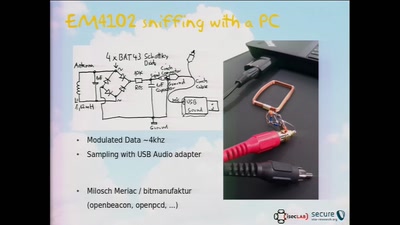
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
46 min