Search for "Seth Hardy" returned 901 results
46 min
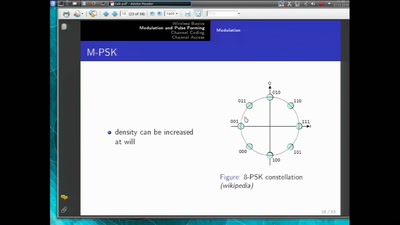
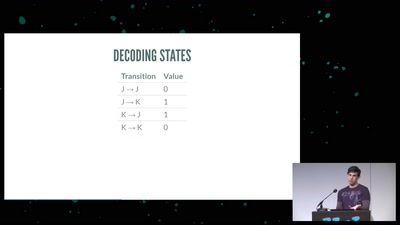
Basics of Digital Wireless Communication
introduction to software radio principles
58 min
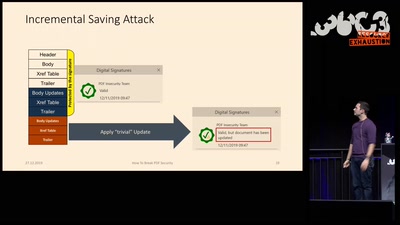
How to Break PDFs
Breaking PDF Encryption and PDF Signatures
55 min
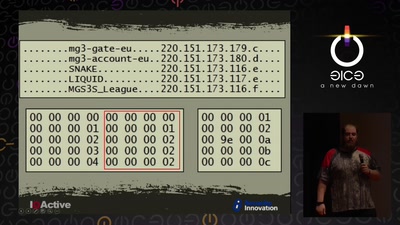
Cyber Necromancy
Reverse Engineering Dead Protocols
60 min
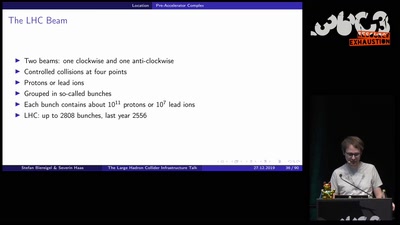
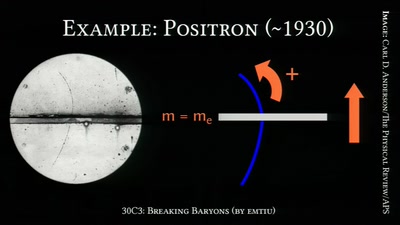
Breaking Baryons
On the Awesomeness of Particle Accelerators and Colliders
33 min
Hacking as Artistic Practice
!Mediengruppe Bitnik about their recent works
113 min
Das Bits&Bäume-Sporangium
8 Mikrokosmen, 8 Expert*innen, je 8 Minuten zu…
60 min
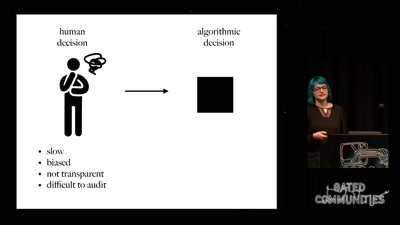
Prediction and Control
Watching Algorithms
64 min
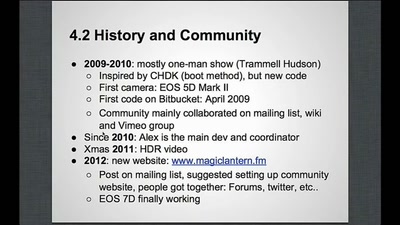
Magic Lantern
Free Software on Your Camera
55 min
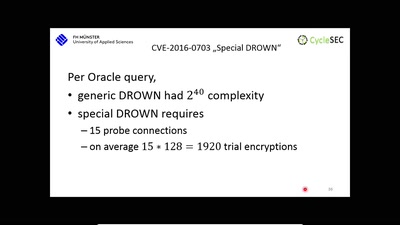
The DROWN Attack
Breaking TLS using SSLv2
62 min
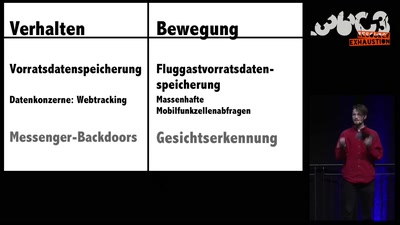
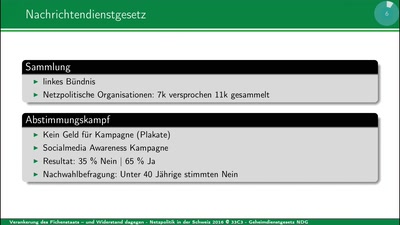
Netzpolitik in der Schweiz 2016
Grundrechte per Volksentscheid versenken
60 min
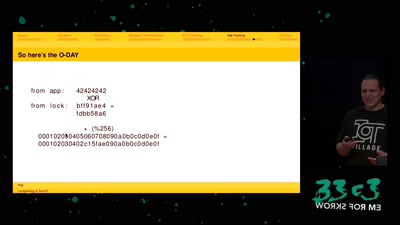
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…
57 min
Hello World!
How to make art after Snowden?
26 min
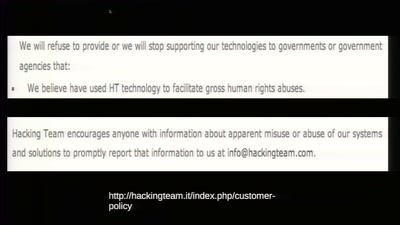
Technomonopolies
How technology is used to subvert and circumvent…
57 min
No USB? No problem.
How to write an open source bit-bang low-speed USB stack…

56 min
Household, Totalitarianism and Cyberspace
Philosophical Perspectives on Privacy Drawing on the…
46 min
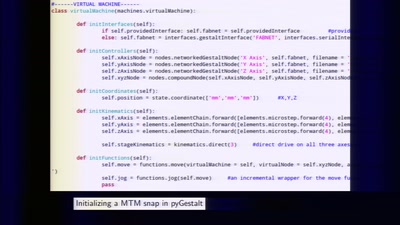
Making machines that make
rapid prototyping of digital fabrication and…
45 min