Search for " Leo" returned 1822 results
38 min
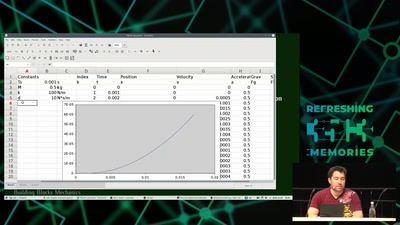
Modeling and Simulation of Physical Systems for Hobbyists
Essential Tools for Developing, Testing and Debugging…
39 min
Venenerkennung hacken
Vom Fall der letzten Bastion biometrischer Systeme

31 min
Extended DNA Analysis
Political pressure for DNA-based facial composites
33 min
Robot Music
The Robots Play Our Music and What Do We Do?
31 min
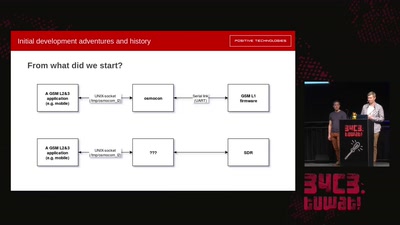
Running GSM mobile phone on SDR
SDR PHY for OsmocomBB
38 min
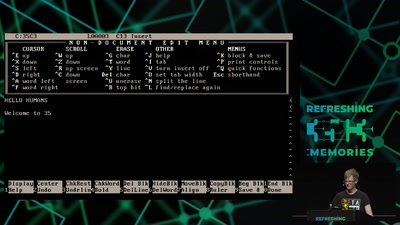
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
28 min
Welcome to the Anthropocene?
(Did) We Accidentally a New Geological Epoch(?)
32 min
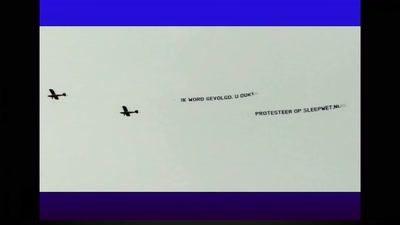
Fuck Dutch mass-surveillance: let's have a referendum!
Forcing the Netherlands to publicly debate privacy and the…
54 min
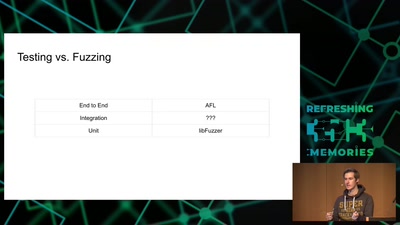
Attacking Chrome IPC
Reliably finding bugs to escape the Chrome sandbox
53 min
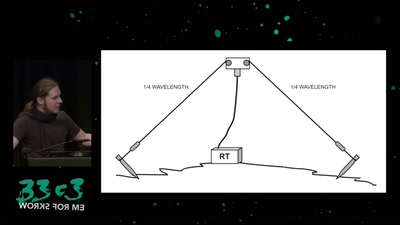
Surveilling the surveillers
About military RF communication surveillance and other…

39 min
Hacking the Czech Parliament via SMS
A parliamentary drama of 223 actors

43 min
Microtargeting und Manipulation
Von Cambridge Analytica zur EU-Wahl
60 min
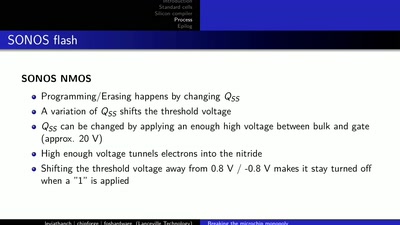
LibreSilicon
Decentralizing semiconductor manufacturing
30 min
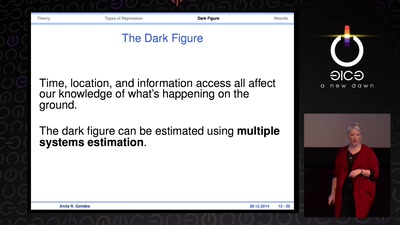
Information Control and Strategic Violence
How governments use censorship and surveillance as part of…

30 min
apertus° AXIOM
The first Open Source Cinema Camera
51 min
How to drift with any car
(without your mom yelling at you)
30 min
On Computing Numbers, with an Application to Problems of our Society
Journalism ♥ Computer Science

32 min