Search for "Inc.)" returned 11620 results
138 min
Enemies of the State: What Happens When Telling the Truth about Secret US Government…
Blowing the Whistle on Spying, Lying & Illegalities in the…

5 min
BGP und OSPF
Redistribute BGP in OSPF mit BIRD, externe OSPF Routen,…
24 min
Responsible Disclosure; How to make your school a safer place.
Story of a 15 year old hacker in collaboration with his…
51 min
The JPEG is dead! Long live the JPEG!
A tour de force of major developments in open source image…
59 min
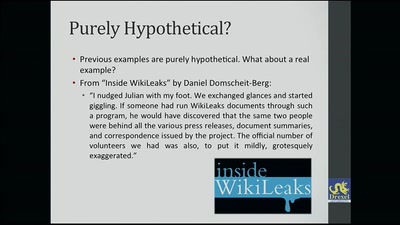
Deceiving Authorship Detection
Tools to Maintain Anonymity Through Writing Style & Current…
58 min
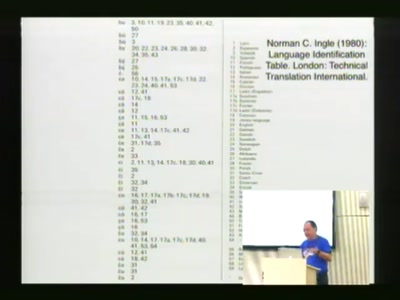
Linguistic Hacking
How to know what a text in an unknown language is about?
29 min
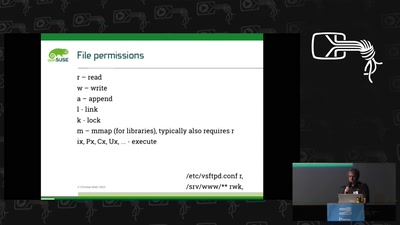
AppArmor Crashkurs
Lerne in unter einer Stunde, AppArmor-Profile zu erstellen…
30 min
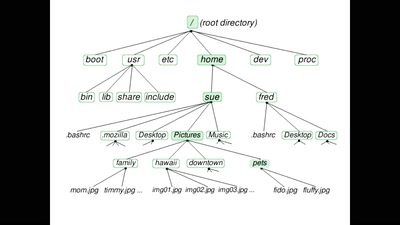
Sourcery: a multi-architecture root file system that is mostly source
Build images that boot on multiple architectures, and that…

87 min
OPENCOIL – A Roaming Speedshow
or the fine art of appropriating inductive charging pads in…
33 min
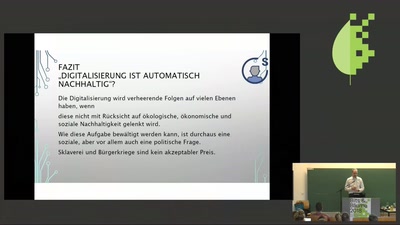
Vorstellung der Studie "Digitalisierung und Nachhaltigkeit" und Buchvorstellung "Der…
Status Quo der Nachhaltigkeitsdefizite in den Bereichen…
52 min
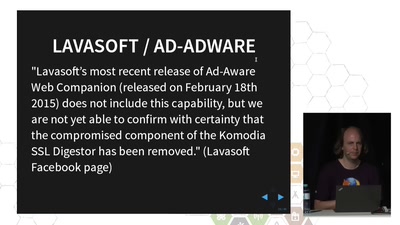
TLS interception considered harmful
How Man-in-the-Middle filtering solutions harm the security…
18 min
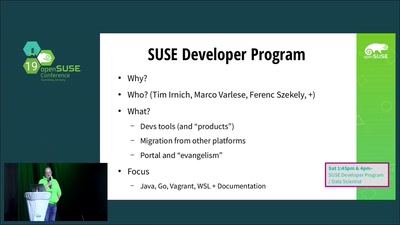
YaST – Yet another SUSE Talk?
Or how are SUSE and the openSUSE community interacting…

57 min
OpenSolaris für Linuxer
Eine Einführung in das Sun-Betriebssystem aus der Sicht…
113 min
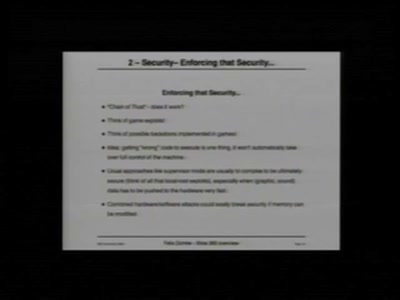
"Xbox" and "Xbox 360" Hacking
17 Mistakes Microsoft Made in the Xbox Security System &…

21 min
Brot selber backen
Wenn ihr keine Lust habt beim Bäcker in der Schlange zu…
45 min
AppArmor Crashkurs
Lerne in unter einer Stunde, AppArmor-Profile zu erstellen…
64 min
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…
71 min
Estonia and information warfare
What really happened in Estonia, and what does it mean to…
55 min
Graphs, Drones & Phones
The role of social-graphs for Drones in the War on Terror.
62 min
Medical Security Nightmares
Things Hackers don't want to see as a patient in a hospital
55 min
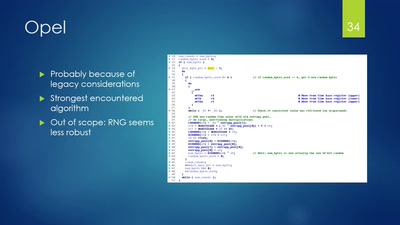
Vehicle immobilization revisited
Uncovering and assessing a second authentication mechanism…
66 min
BOLSONARO IS AN ENVIRONMENTAL CATASTROPH!
How the rise of bolsonsarism culminate in the Burning of…

70 min
Attacking IoT Telemetry
A study of weaknesses in the pipeline of rapidly advancing…

36 min
Sim Gishel
A singing and dancing robot build to take part in casting…
55 min