Search for "Mo" returned 10573 results

41 min
Illumos uns gibt es noch
was läuft so im lande von Illumos
54 min
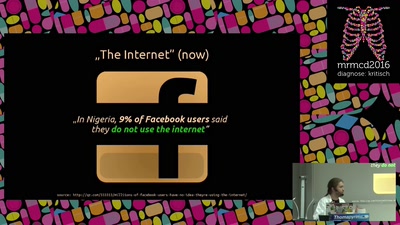
Coronary bypass at the heart of the Intertubes, badly needed
Why and how to redecentralize the Net

60 min
On working memory and mental imagery
How does the brain learn to think?
58 min
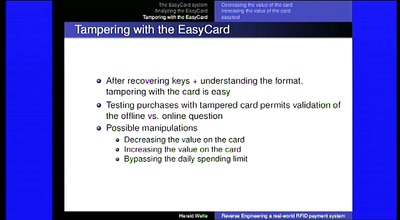
Reverse Engineering a real-world RFID payment system
Corporations enabling citizens to print digital money
74 min
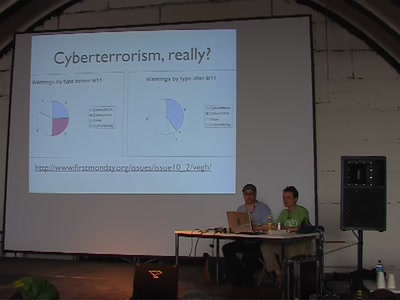
Legal, illegal, decentral: Post-hacker-ethics cyberwar
Applied loss of control to hacker-ethics?
57 min
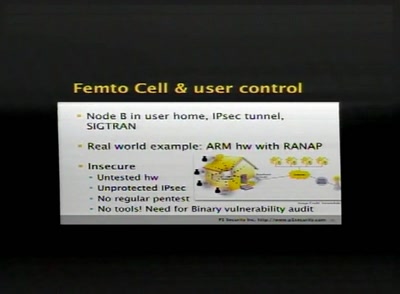
SCCP hacking, attacking the SS7 & SIGTRAN applications one step further and mapping the…
Back to the good old Blue Box?

69 min
Die alternativlose Umverteilungs-Gala!
mv -r grunewald/money everyone/money
60 min
ALTAIR, IMSAI, Dazzler und CP/M
Die Anfänge der individuellen Computergrafik
64 min
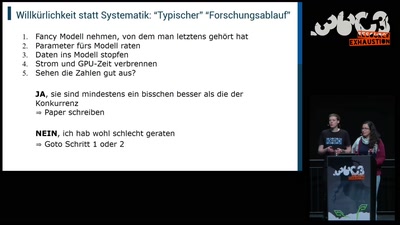
Der Deep Learning Hype
Wie lange kann es so weitergehen?
60 min
Desperately Seeking Susy
A farewell to a bold proposal?

49 min
Hacking Data Retention
How bureaucrats fail to fight terror
54 min
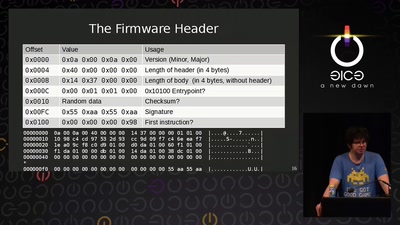
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?
43 min
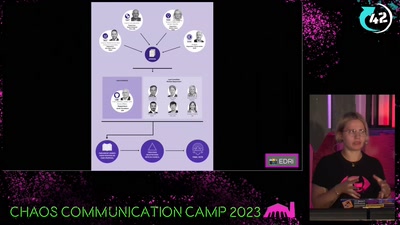
Chat-Control
now is the time to take action!
61 min
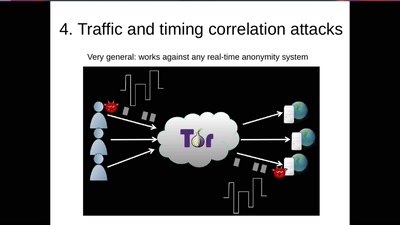
Tor de-anonymization techniques
How people have lost their anonymity? Let's study…
43 min
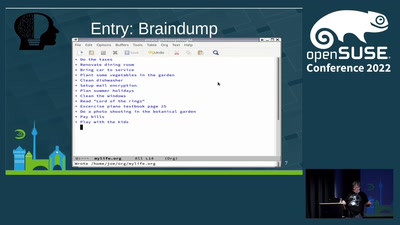
Org mode: Manage your life in plain text
Use Open Source to make your life easier

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
40 min
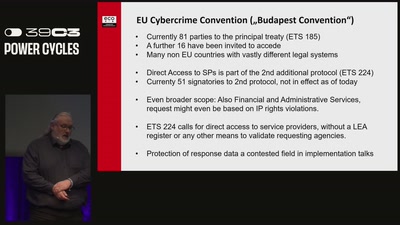
Live, Die, Repeat
The fight against data retention and boundless access to…
56 min
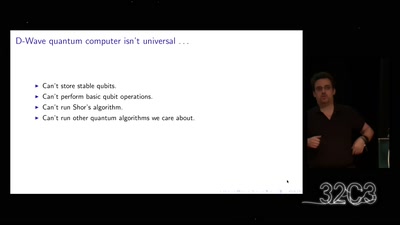
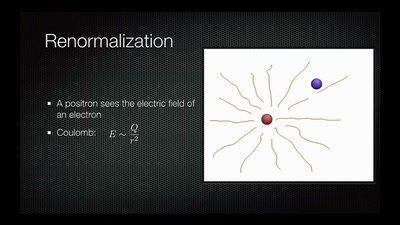
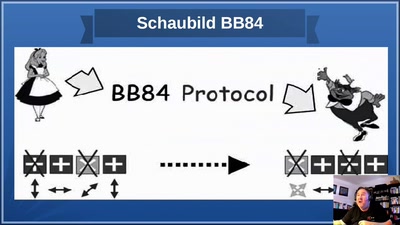
God does not play dice!
an introduction to quantum cryptography for sysadmins and…
60 min