Search for "Mark" returned 1199 results
57 min
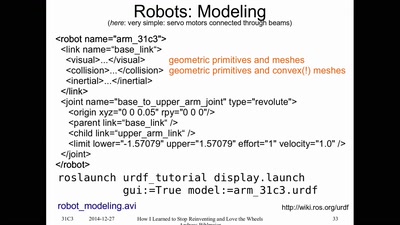
How I Learned to Stop Reinventing and Love the Wheels
or having FUN with (home/hackerspace) robotics
58 min
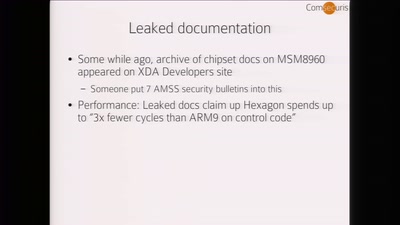
Baseband Exploitation in 2013
Hexagon challenges
58 min
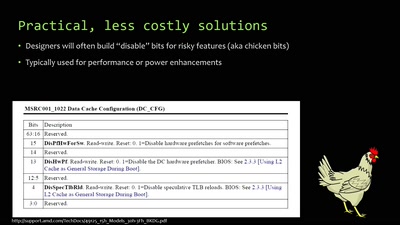
When hardware must „just work“
An inside look at x86 CPU design
113 min
Methodisch inkorrekt!
Die Wissenschaftsgala vom 33C3
64 min
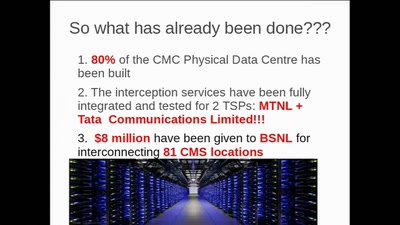
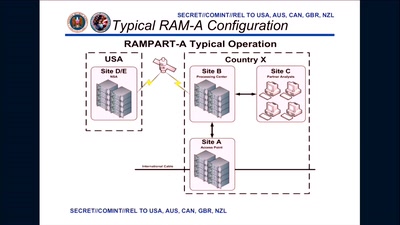
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…
55 min
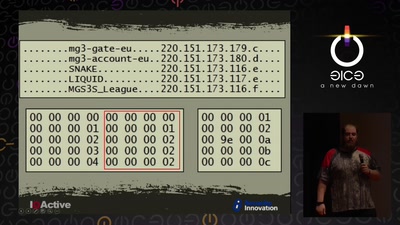
Cyber Necromancy
Reverse Engineering Dead Protocols
60 min
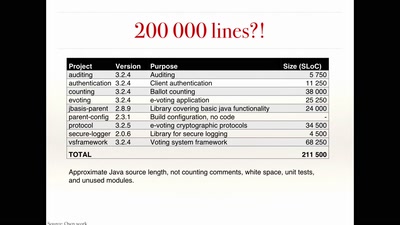
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation
57 min
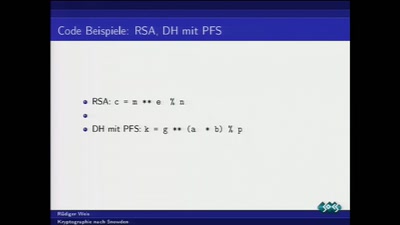
Kryptographie nach Snowden
Was tun nach der mittelmäßigen Kryptographie-Apokalypse?
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
61 min
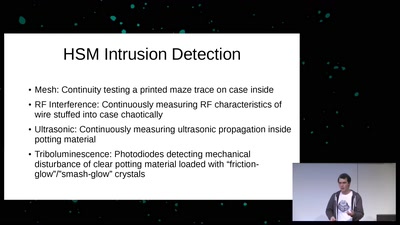
Untrusting the CPU
A proposal for secure computing in an age where we cannot…

61 min
Dead Man Edition
Auf dem Weg zu fairer Elektronik am Beispiel der Elkos …

59 min